Best practices for cloud services
Introduction
Today most people have a smart phone, tablet or PC. Some years back we stored our photos on backup media such as CD or DVDs. Today different companies compete about getting access to our files. Most people today doesn’t react when a new “app” is installed and permissions is asked to our pictures, private messages or even our microphone.
Even the big companies is vulnerable to hackers
Microsoft, Google and Apple has all been hacked and sensitive data has been compromised. Most “unlucky” supplier (when looking at cloud storage); seems however to be Dropbox. Maybe that’s because they don’t have the same strength as the big competitors. Maybe it’s because a succeeded attack would give access to sensitive, unencrypted data. This is obviously a wet dream for hackers and a goldmine for surveillance departments all over the world.
http://www.slideshare.net/ibmsecurity/remote-exploitation-of-the-dropbox-sdk-for-android
More reading: https://blogs.dropbox.com/dropbox/2014/05/web-vulnerability-affecting-shared-links/
Online storage
| Dropbox | OneDrive | Google Drive | iCloud | |
| Transfer Encryption | 256 bit AES[1] | SSL/TLS[6] | SSL/TLS[3] | 128 bit AES*[7] |
| Remote Data encryption | Yes[1] | Yes[6] | No[2] | Yes[7] |
| Local Data encryption | No | No | Mobile[3] | No |
| Data recovery | Yes[5] | Yes[8] | Yes[4] | Yes[7] |
| Two way authentication | Yes | Yes | Yes | Yes |
| Anonymity | Yes | No | No | No |
| * “A minimum of 128-bit AES encryption” | ||||
Protecting your account
1. Two step authentication
Two step authentication is always a good idea. Even if the password is in the hands of hackers or other unauthorized users; you will have to verify each login using a external service such as SMS, second password or a temporary code generated from application.
You can read more about this at your cloud provider:
Dropbox: https://www.dropbox.com/help/363
Microsoft/OneDrive: http://www.windowscentral.com/make-microsoft-account-more-secure-two-step-verification
Google/Google Drive: https://www.google.com/landing/2step/#tab=how-it-protects
Apple/iCloud: https://support.apple.com/en-us/HT204152
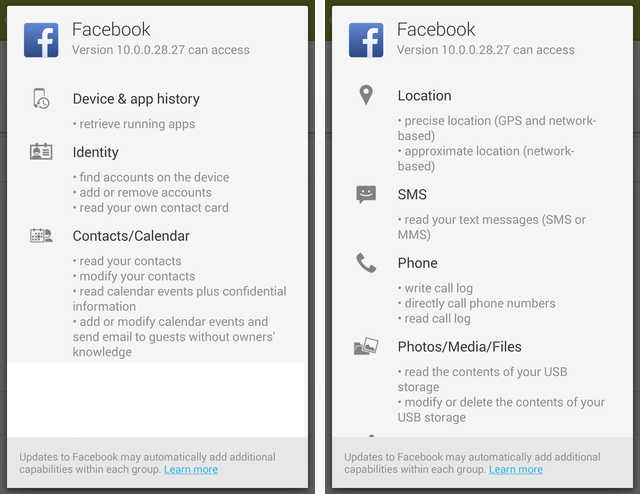
2. Check permissions
Check which applications you have allowed to read/write from your cloud service.
Dropbox
Login à Settings à Security à Apps linked
Google Drive
Login à Account à Security tab à click View All
(under Account permissions)
OneDrive and iCloud
We haven’t found any generic way to achieve this yet.
3. Vary & Protect your password
- Don’t save passwords in your browser. Their usually very bad protected and many times stored without encryption.
- Don’t use the same password as your login. No operating system is protected from extracting and cracking hashes.
- Use different passwords. Forum and communities is hacked all the time so make sure to at least have one password which you only use for the most sensitive accounts, such as your e-mail and cloud access
4. Encrypt content
Disk encryption
What happens when you drop your phone or even worst your laptop? Recovering a password is just a matter of hardware and time. Most cellphones
is not totally encrypted by default, which means that unless your local data is encrypted, they can easily be accessed by anyone.
Microsoft / Windows: https://technet.microsoft.com/en-us/windows/dn468672.aspx
Google / Android: http://www.ghacks.net/2012/10/13/encrypt-all-data-on-your-android-phone/
Apple: / iOS: https://s3.amazonaws.com/s3.documentcloud.org/documents/1302613/ios-security-guide-sept-2014.pdf
Container encryption
Creating a container (vault) where you can store your sensitive files is a good solution since it will also protect your files, no matter where their stored.
+ Your files is protected from physical theft, hackers and all other unauthorized access.
– You will need to download or synchronize the entire container to access one file.
– Only the files in the container is protected.
“Google Drive does not currently encrypt files on the server. Our team and our company take the security and privacy of our users very seriously. For example, we support 2-factor authentication, and as Julio mentioned, all transmissions to and from your device using HTTPS and TLS. However, you can encrypt a file (or all your files) before you add it to Google Drive, and Drive will sync any file (whether it’s encrypted or not) to all your devices.” [2]
The favourite of applications for creating an encrypted container was TrueCrypt, which has reached end of life. There are many alternatives and a nice compilation can be found at: http://arstechnica.com/civis/viewtopic.php?t=1245367
Text encryption
There is many applications for encrypting and decrypting text chunks. For storage of text, e.g. using Evernote this is the optimal solution. We haven’t tested any applications for cross platform encryption or decryption, so we have no suggestions at current time.
Important: Make sure that the application you using for this does not save any cached versions of the file. Also make sure that the application used for reading the unencrypted content does not save any local cached version of the file.
+ Offers same protection as using a container
+ You can use many keys
– Indexing and searching for files will be harder. You need to have a good structure to find what you’re looking for.
References
[1] – https://www.dropbox.com/security
[2] – https://productforums.google.com/forum/#!msg/drive/6AdrOutSoFU/sgixqxX3yfQJ
[3] – https://www.google.com/intx/en/work/apps/business/driveforwork/
[4] – https://support.google.com/drive/answer/2405957?hl=en
[5] – https://www.dropbox.com/help/11
[6] – https://products.office.com/en-us/business/office-365-trust-center-cloud-computing-security
[7] – https://support.apple.com/en-us/HT202303
[8] – http://windows.microsoft.com/en-us/onedrive/lost-missing-files