Tool: How long time does it take to crack a password?
How long time does it take to crack a password
We made a little tool which can help you with time estimations when securing your customers server environment or preparing to recover a password. The tool we have arranged for you – shows how much a little research can do for the operational time. You find it here and in the bottom of the article.
Below we will make some calculations based on LM Hashes (Old windows) and NTLM Hashes (Current systems). LM Hashes is converted to uppercase at time of save in database and when comparing, eg. when user logins to system – with that information we will not test our password against both upper case and lower case (since it would be of no use).
The more we know about the environment – the better we can prepare a future attack.
Would would happened if you used 10 computers with 18 cores instead? (prob. about 1800%)? Today it’s possible to rent virtual servers for making a linked network to crack passwords. I have actually asked if I can decrypt passwords and the result has always been that what I do is up to me from the same moment I bought the server on hourly based.
Password statistics
Mark Burnett, Mark Burnett is a security consultant, author, and researcher who specializes in hardening Microsoft Windows-based servers and networks. When he released an analysis[1] based on more than 6,000,000 passwords (merged from most major hacked sites the last years); the result was nothing less than a warning signal to the industry. The average passwords was 7-8 characters, 91% of all passwords could be found in the top 1000 most common passwords and when including the larger list with 10.000 common passwords only 0.18% of all users had an unique password.
Aviv Ben-Yosef, an software developer from Israel generated an article[2] with statistics from a password list that lolsecs released[3] that included 62.000 passwords. The pattern is similar to Mark Burnetts report. An average password has the length of 7-8 characters, most common is 123456, 123456789 and password.
What makes a secure password?
It’s not an easy question to answer. I would say that the password length is the single most important factor, together with character set.
Hardware
Rainbow tables is one of the most effective ways to crack passwords and they remind of lookup tables, which means you trade CPU power for storage. You can find tools & rainbow tables at our Library page by clicking here. Today most available rainbow tables is generated for common characters, digits and symbols – which means their ineffective if the password is using characters from smaller countries. Rainbow tables takes long time to generate and if their generated for complex passwords they will consume a big hard disk.
GPU
The GPU is a CPU on the graphic card. It’s designed for doing math calculations and therefor much faster than a CPU, even with many cores. When using rainbow tables which has been optimized for the GPU you can crack passwords up to 8 characters in less than a day using an average gaming computer. You can find some popular tools at our Library by clicking here.
CPU
The power in CPU cracking is if you can connect many nodes together and build a network. Today there’s multiple sites** which can give you a dedicated virtual server with 1-20 cores for less than a 1$ / hour. Using 10 dedicated appliances with 18 cores each would give you the power of close to 180 computers for less than 10USD.
**eg. Digitalocean, amazon, codero
How long time does it take to crack a password?
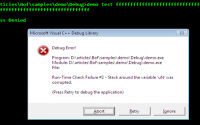
To keep it simple we created a tool for you which you can find here. We will use it and assume that we can’t use a dictionary and that we have an average computer, with only one cpu/no extra cores, which can handle 20000000 combinations / second – and performing a brute-force attack. But back to the question; about how long time does it take to crack a password?
Password length: 7
All 95 writable ASCII characters gives us 75144747810816 combinations and would be cracked in just one month and a few weeks. Older windows systems supports LM Hashes, so in that case we can remove the mixed character set and results in 8235430000000, which would take less than five days to crack. That’s a little scary since we know from password statistics* that an average password length is 7-8 characters.
Password length: 8
All 95 writable ASCII characters gives us 6634204312890625 combinations and would be cracked in 10 years 6 months 9 days 5 hours 43 minutes if it was the last tested combination. For LM Hashes we can remove either lower case or upper case character set (since windows password vault saves them in upper case); which reduces the total number of combinations into 513798374428641 which “only” would take up to 9 months 27 days 8 hours 5 minutes.
Last edited: 2014-08-01